

Protecting Your Organization from the Latest Wave of Cyberattacks Exploiting 'CitrixBleed' CVE-2023–4966
Protecting your organization from the latest wave of cyberattacks exploiting 'CitrixBleed' is crucial to safeguard your sensitive data and maintain the integrity of your systems. 'CitrixBleed' is a vulnerability found in Citrix Application Delivery Controller (ADC) and Gateway devices that allows remote attackers to execute arbitrary code.
Reports indicate that the targets of these cyberattacks have included major entities such as Boeing in the aerospace sector, ICBC, the world's largest bank, DP World, one of the largest port operators globally, and the international law firm Allen & Overy.
A substantial number of organizations are still susceptible to the vulnerability, officially identified as CVE-2023-4966 and nicknamed "CitrixBleed." The majority of these vulnerable systems are situated in North America, as reported by the nonprofit threat tracker, Shadowserver Foundation. CISA, the cybersecurity agency of the U.S. government, has issued a warning through an advisory, urging federal agencies to promptly patch the actively exploited flaw.
To protect your organization, follow these steps:
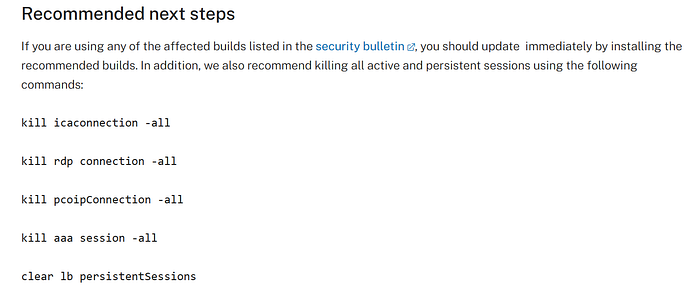
- Patch and update: Ensure all Citrix ADC and Gateway devices are updated with the latest security patches. Citrix has released patches to address the 'CitrixBleed' vulnerability, and it is essential to apply them promptly.
- Implement access controls: Restrict access to Citrix ADC and Gateway devices by implementing strong access controls. This includes enforcing strong passwords, implementing multi-factor authentication (MFA), and limiting access to only authorized personnel.
- Monitor network traffic: Employ network monitoring tools to detect any suspicious activity or attempts to exploit the 'CitrixBleed' vulnerability. Regularly review logs and alerts to identify any potential signs of compromise.
- Segment your network: Implement network segmentation to isolate critical systems and limit the impact of a potential breach. By separating your network into different segments, you can restrict lateral movement and contain any potential attacks.
- Train employees: Educate your employees about the 'CitrixBleed' vulnerability and the importance of cybersecurity best practices. Train them to recognize phishing attempts, suspicious emails, and other social engineering techniques that could be used to exploit vulnerabilities.
How to Patch?
Head Here : https://www.netscaler.com/blog/news/cve-2023-4966-critical-security-update-now-available-for-netscaler-adc-and-netscaler-gateway/
Additionally, it is recommended to stay updated with the latest cybersecurity news and advisories from reputable sources such as Citrix's official website, security blogs, and forums. Regularly review security bulletins and apply any necessary updates or mitigations.
By following these steps and maintaining a proactive approach to cybersecurity, you can significantly reduce the risk of falling victim to cyberattacks exploiting 'CitrixBleed'.
Related Posts
© 2024 Invastor. All Rights Reserved




User Comments
User Comments
There are no comments yet. Be the first to comment!