

Chapple.ai and Data Security: Ensuring Trust in AI Solutions
As businesses increasingly rely on AI solutions for data analytics and decision-making, the importance of data security cannot be overstated. Chapple.ai stands as a pioneer not only in advanced AI solutions but also in prioritizing robust data security practices. This article explores how Chapple.ai ensures trust in its AI solutions by placing a strong emphasis on data security.
Commitment to Data Security:
Chapple.ai's commitment to data security is foundational to its mission. The platform recognizes the sensitive nature of the data it handles and prioritizes the implementation of stringent security measures. This commitment is woven into every aspect of Chapple.ai's operations, ensuring that users can trust their data to be handled with the utmost care.
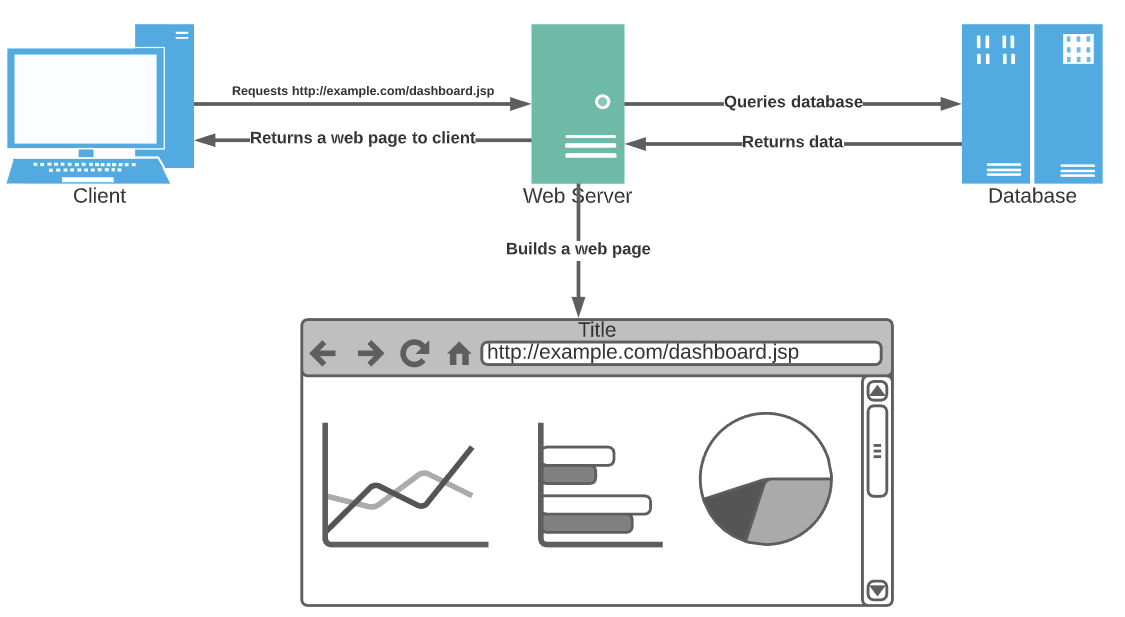
Secure Data Storage and Transmission:
Chapple.ai employs secure data storage practices to safeguard user information. Data is stored in encrypted formats, protecting it from unauthorized access. Additionally, the platform ensures the secure transmission of data between users and the Chapple.ai servers, utilizing encryption protocols to prevent interception or tampering during transit.
Encryption Technologies:
Encryption is a cornerstone of Chapple.ai's data security strategy. The platform leverages state-of-the-art encryption technologies to protect data at rest and in transit. This ensures that even if unauthorized access is gained, the encrypted data remains indecipherable, maintaining the confidentiality and integrity of the information.
User Authentication and Authorization:
Ensuring that only authorized users access sensitive data is paramount. Chapple.ai implements robust user authentication and authorization protocols. This includes multi-factor authentication measures and role-based access controls, limiting access to data based on user roles and responsibilities. These measures contribute to a secure and controlled data environment.
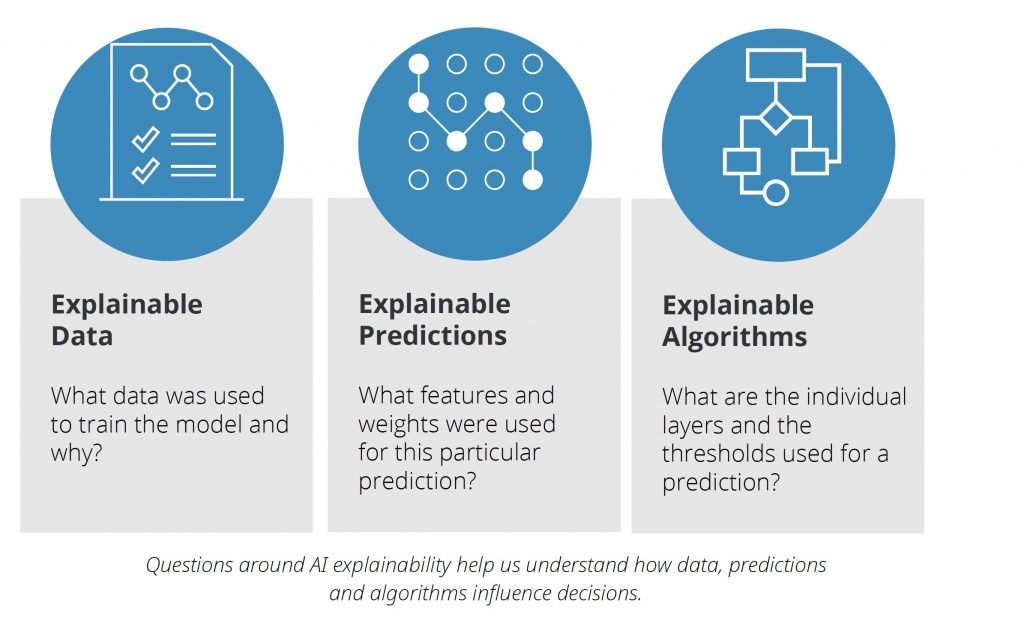
Transparent Data Practices:
Transparency is a key element in establishing trust. Chapple.ai maintains transparent data practices, clearly outlining how user data is collected, processed, and stored. By providing users with visibility into these processes, Chapple.ai aims to build trust and confidence in its commitment to safeguarding user information.
Ethical Use of Data:
Beyond technical measures, Chapple.ai emphasizes the ethical use of data. The platform ensures that user data is used responsibly and in accordance with user expectations. Ethical considerations guide the development and deployment of AI models, fostering a culture of trust and responsible data usage.
Continuous Improvement and Adaptation:
Chapple.ai views data security as a dynamic aspect of its operations. The platform is committed to continuous improvement, regularly updating its security measures to stay ahead of emerging threats. This adaptive approach ensures that Chapple.ai remains resilient in the face of evolving cybersecurity challenges.
Price:
Paid plans start from $19.99
Conclusion:
In the realm of AI solutions, data security is non-negotiable. Chapple.ai's proactive approach to data security, encompassing encryption, compliance, transparency, and ethical use, ensures that users can trust the platform with their valuable data. By prioritizing data security, Chapple.ai not only safeguards user information but also contributes to building a foundation of trust and reliability in the realm of AI-driven solutions.
Contact us:
Website: https://chapple.ai/
Facebook: https://www.facebook.com/chappleai/
Twitter: https://twitter.com/chappleai
Related Posts
© 2024 Invastor. All Rights Reserved





User Comments
User Comments
There are no comments yet. Be the first to comment!